Healthcare’s MSSP
Threat detection and response—protecting the business of healthcare
The Clearwater Security Operations Center (SOC) works 24x7x365 to keep your organization operating without disruption.

Detect and Mitigate Threats Before They Become a Crisis
You need the ability to detect and contain a threat actor before they attack, causing a breach and harming your business.
Additionally, you need to address threat detection and response requirements in a way that meets cyber insurance carriers’ requirements and facilitates compliance obligations for PCI, HITRUST, and SOC 2.
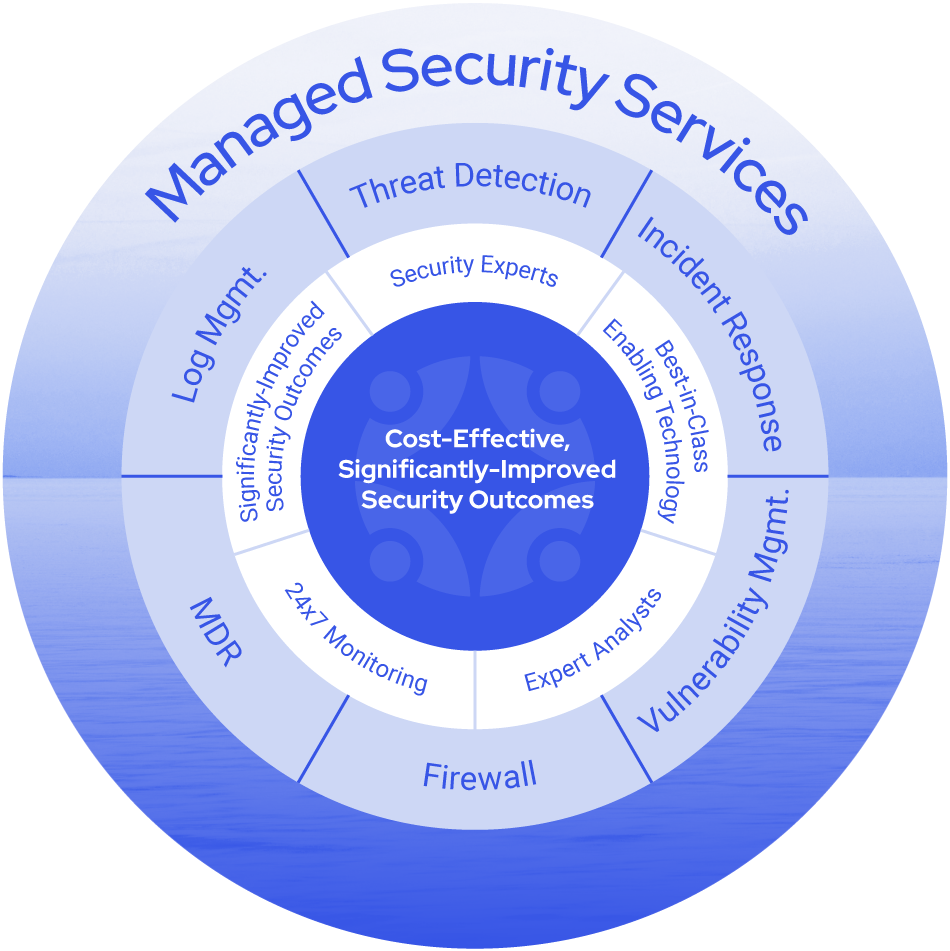
That’s what you get with Clearwater’s managed security services. Powered by industry-leading EDR tools and our proprietary security orchestration, automation, and response platform, our 24x7x365 SOC provides firewall management, continual threat detection, attack monitoring, and incident response in cloud and on-premise environments.
Effective Managed Security and Threat Detection for Healthcare
Remove the overhead and burden that comes with a flood of false positives and requires constant upkeep.
Managed Threat Detection & Response
In tandem with EDR technology, licensing, set-up, and continuous management are all part of our service.
Firewall Security Management
Update your defenses and benefit from our experts in healthcare network segmentation to ensure ongoing protection.
Log Management & Threat Detection
Our experts tune log configurations and collect, consolidate, search, and validate log retention for compliance needs.
Vulnerability Management
Ongoing scanning identifies security exposure points and prioritization guidance based on your unique environment.
Clearwater is a healthcare-focused Managed Security Service Provider (MSSP) that understands the unique dynamics across all segments of the industry. Our team actively responds to events and hunts for threat indicators. You have complete visibility of all monitored system activity with access to the same portal that our analysts use, providing full transparency to our services with informative dashboards that equip you with real-time data regarding the security posture of your environment.
We leverage event signals and threat intelligence to deliver immediate insights that guide the next best action. As a result, we stop bad actors in their tracks before their actions result in a crisis. We give ongoing reviews and recommendations to help you continually improve your security posture.
Featured Experts
Your Clearwater Managed Security Services team is led by cybersecurity experts who know what it takes to keep your organization safe around the clock.

SME Highlight
Steve Akers
Steve has over 25 years of experience in cybersecurity and compliance and more than 15 years in security and consulting services.

SME Highlight
Dave Bailey, CISSP
Dave Bailey is Vice President of Security Services at Clearwater and leads the managed, professional, and consulting services for the […]
Contact us to learn more about Clearwater
Why Clearwater?
Security is complex, and HIPAA or HITRUST compliance is not enough
Regardless of size or type of business, organizations across the healthcare spectrum are all competing for the expertise needed to mitigate cyber threats and develop strategies to protect data within entwined environments.
Clearwater knows security, and we are continuously optimizing our 24/7 managed security services to improve outcomes and provide a path to helping you become more secure, compliant, and resilient.

Physician Practice Management/Ambulatory Care
Multiple locations supporting various healthcare services can achieve centralized support with threat detection and response and 24/7 security operations. Clearwater helps to protect the investments and growth strategies for extended clinical care and wellness services.

Digital Health
Healthcare digital innovators can protect data and operations as they grow their value. Clearwater experts thoroughly investigate all events, providing clear insight into your threats and paths for reconciliation that are risk-based, not overkill.

Medical Device/MedTech
Protect the supporting environments and systems that interact and connect to medical devices and diagnostic systems, including healthcare MDR. Clearwater managed security services identify behavioral anomalies and detect threats early, minimizing operational technology systems risk.
ClearAdvantage®
Subscribe to our Managed Security Services program separately or as part of our ClearAdvantage® program.
Featured Resources
Connect
With Us



