
Some service providers forget that their business is about supporting clients and building long-term relationships. Not every relationship should continue if there are critical warning signs. Feeling locked in or trapped in a sub-par relationship is not something you have to accept. There are plenty of options as the market is growing and evolving but finding the right fit might take time.
From IDC the evolution of Managed Security Services ranges from device management to the more advanced and skilled managed detection and response.
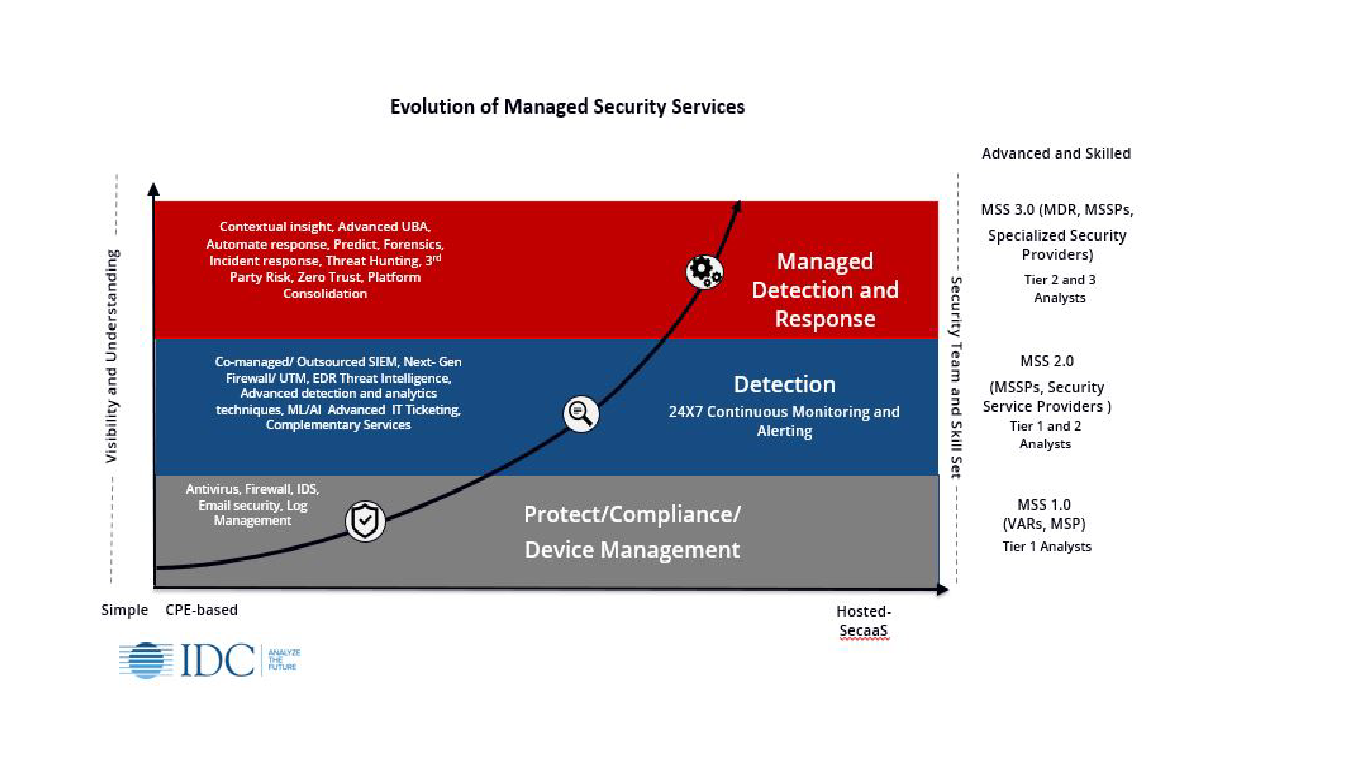
Some top-tier MSSPs (Managed Security Service Providers) would have you believe that their value is in being able to manage your new [insert cool technology product name here], or existing security stack, in your environment on your behalf. The clients get the most value from their past investments and the ability to now re-deploy staff onto other projects. This works for large enterprises that had the initial technology budget and staff to research and direct which investments to make, deploy the appropriate solutions, and align security operations based on their needs. However, these companies come to realize their human capital is constrained and could be better utilized focusing on higher-order business. This is especially true as security expertise and threat-hunting analysts are in premium demand.
The various models and growth in the MSSP industry are being fueled by the ability to serve organizations of all sizes, helping them to achieve better security outcomes. Moving a client from having a basic security framework, an MSSP can immediately, advance the companies protection and detection capabilities to those of much larger organizations.
Considering the several types and models for MSSPs, companies should aim for those who do more than just take on security device management. Those that have architected for the highest tier, from the IDC chart, can give advantages to smaller companies that did not or could not invest in security technology in the past. Providing managed detection and response from all angles of security operations increases the visibility into malicious behavior, and threat-hunting details needed to act quickly. Ideally, an MSSP should be able to provide service across the following assets:
Endpoints: The largest attack surface comes from end-user laptops and workstations, especially with the shift to remote work.
Servers: The most critical systems in your organization.
Network: The point that gives the widest access to your companies’ resources.
Specialized security providers have proliferated around each of these pillars along with providers of log management with threat detection. Some vendors of these solutions have created MSSP units to provide the management, maintenance, and respond to events and incidents on behalf of their customers. However, because they are focused only on one area or leveraging point solutions, they cannot move easily to provide broader security and threat detection coverage through a comprehensive end-to-end security solution.
One thing everyone can agree on is that focusing on detection and response is critical to quickly act and mitigate before any damage is done. Here is a simple breakdown of what this requires – without getting into technology acronyms.
- Especially in today’s threat landscape, 24×7 active security operations coverage is needed if a business hopes to stay protected
- Proactive threat hunting vs. responding to security alerts
- Extended access across the spectrum of security data vs. looking at only specific security events
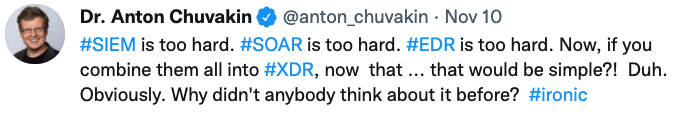
You may recognize this as Extended Managed Detection and Response (XDR) or you may not. Some believe that XDR refers to a platform that facilitates these services provided by a single security solution vendor. Others believe that this is an evolutionary step where XDR can fulfill where the promise of Security Incident and Event Management (SIEM) solutions fell short. This can be a vendor delivering a platform that integrates the extended security events into view for threat hunting activities. And, of course, there are several other assumptions about what XDR represents. I am pointing this out as many service providers focus on providing XDR, and there is not really a clear and common definition in the market these days. It is not the silver bullet to solve all security problems.
As Anton Chuvakin tweeted:
At the end of the day, prospects must assess if they are staying the course with their security operations and/or current MSSP or need to change. All prospects have pain and business drivers they need to solve.
Common problems:
- Cannot staff security operations 24/7/365 and on-call pager-duty is burning my staff out
- Experienced security analysts are too expensive
- Security spending keeps growing but my security incidents have not decreased
- Even with an MSSP I am getting lots of alerts, but few answers
- I do not have much visibility into what my provider is doing and when there is an incident that matters
To help organizations we have put together a guide with 5 Tips on How to Evaluate an MSSP. It gives details on what to expect and what to ask if you are looking to explore if an MSSP is the right direction or are unsatisfied with the provider you are currently using.
While we have discussed many of the models and technical aspects of choosing an MSSP you cannot forget that at the end of the day it is a relationship. Never should you feel that you are just a number, your questions about the service or event are answered with a condescending tone, and that talking or meeting with a human is the exception and not the norm.
If you would like to learn more about TECH LOCK and meet with our team, schedule a direct meeting today, or take 5 minutes to review our guide on evaluating an MSSP.
