Blog
Insights into today’s security and compliance challenges
Articles
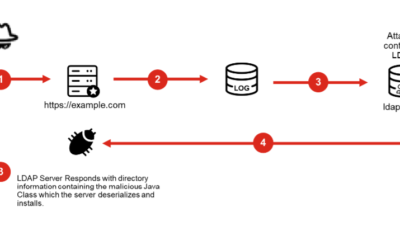
Log4J Exploit Easily leads to Remote Code Execution
Log4J Remote Code Execution (RCE) Exploit has far-reaching implications as it is a highly popular open-source library. Learn what small to mid-sized enterprises can do about this today.
Love Them, or Leave your MSSP for the Right One
There are plenty of MSSP options as the market is growing and evolving but finding the right fit might take time. Read the blog to learn more
Blocking Threats at the Endpoint
Recently, we were questioned about our vendor of choice from a prospect. They asked, “How do you know the efficacy of Fortinet EDR technology solution, and will it protect better than the other vendors?” Read the answer in this blog
Prioritize Critical VPN Vulnerabilities
A joint alert from NSA and FBI itemizes the vulnerabilities that are being used to infiltrate organizations through exposed VPN solutions.
Security for Survival vs. Strategic Security
The unfortunate state of where we are with cybersecurity can be attributed to the decisions we’ve made along the way. There are those who look at security in the most basic form and those who treat security as a strategic initiative that enables their business. However, what security entails is very clear…
SolarWinds Widening Risk
Take Action Now Disconnect or power down SolarWinds Orion products, versions 2019.4 through 2020.2.1 HF1, from their network. Treat all hosts monitored by the SolarWinds Orion monitoring software as compromised by threat actors and assume that advanced...